We have received a number of complaints from customers about a phishing email, which pretends to be sent by us – LiquidNet Ltd., by eNom, or by another legitimate domain registrar. Global phishing attacks are common nowadays. However, this particular one goes one step further, stirring confusion by including a specific domain name that is owned by the given recipient, rather than some random content.

What is the phishing email about?
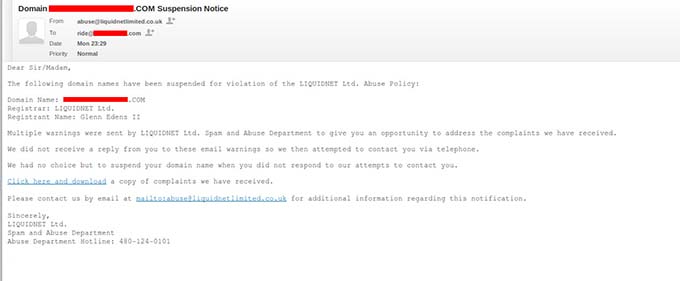
Here is how a phishing email like this looks like (click on the image to expand):
The accurate domain owner information, coupled with the sense of urgency created by the phishers themselves, have caught many users off guard and have prompted them to click on links, which lead to virus-infected websites.
Fortunately, many of the companies hosting the phishing sites have been notified and the harmful pages have been suspended. However, this does not exclude the possibility that other infected pages may still be circulating around.
What should you do when you receive such an email?
First and foremost:
DO NOT CLICK ON ANY OF THE LINKS IN THE EMAIL!
A quick way to verify if the email sender in the header is authentic is to always hover over the link itself to see where it’s going.
In those emails, the sender’s address has been replaced by a legitimate one, but you can easily tell whether the message has come from a notorious phishing location like China.
Here is an example of how a phishing email’s Return-Path header would look like:
Return-Path:
Received: from stu.xjtu.edu.cn
X-EQAUTHUSER: zhhliu@stu.xjtu.edu.cn
Mobile phone users can press and hold the link to see the full URL.
If you are still in doubt, forward any emails you are unsure of to support@resellerspanel.com and we will reply back shortly.

What is the phishing email about?
Here is how a phishing email like this looks like (click on the image to expand):
The accurate domain owner information, coupled with the sense of urgency created by the phishers themselves, have caught many users off guard and have prompted them to click on links, which lead to virus-infected websites.
Fortunately, many of the companies hosting the phishing sites have been notified and the harmful pages have been suspended. However, this does not exclude the possibility that other infected pages may still be circulating around.
What should you do when you receive such an email?
First and foremost:
DO NOT CLICK ON ANY OF THE LINKS IN THE EMAIL!
A quick way to verify if the email sender in the header is authentic is to always hover over the link itself to see where it’s going.
In those emails, the sender’s address has been replaced by a legitimate one, but you can easily tell whether the message has come from a notorious phishing location like China.
Here is an example of how a phishing email’s Return-Path header would look like:
Return-Path:
Received: from stu.xjtu.edu.cn
X-EQAUTHUSER: zhhliu@stu.xjtu.edu.cn
Mobile phone users can press and hold the link to see the full URL.
If you are still in doubt, forward any emails you are unsure of to support@resellerspanel.com and we will reply back shortly.



Comment